Tag Archives: Lookups
Fortinet LDAP/RADIUS Source address with SD-WAN setup
Posted by on June 21, 2023
I found this a neat tidbit of knowledge that I thought I should share.
Created a Fortinet SDWAN setup with many sites – works awesome. Fortinet’s SDWAN is simple, but very effective with some really cool features to help with SLAs.
During this setup, I have Radius, and LDAP servers located across one of the members of the SDWAN (An IPSEC tunnel). As before with tunnels, you would modify the source address in CLI for the destination server. This would make sure requests originate from the interface you are expecting, and will go through the tunnel.
After switching the tunnel to be a member of a SDWAN interface the LDAP/RADIUS requests stopped working. I found another command was needed. This command is needed not only for Radius, and LDAP but also for FAZ, Fortiguard, and dns.
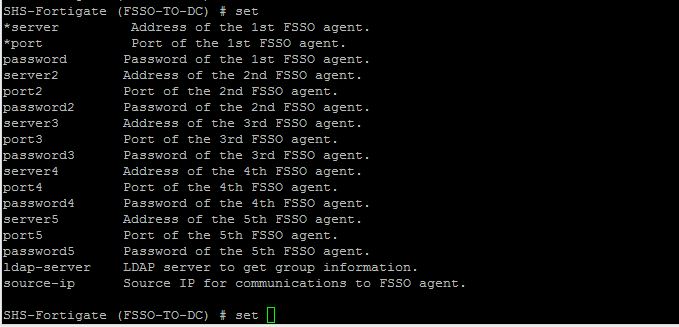
In CLI of both Radius and LDAP servers you will see these options:
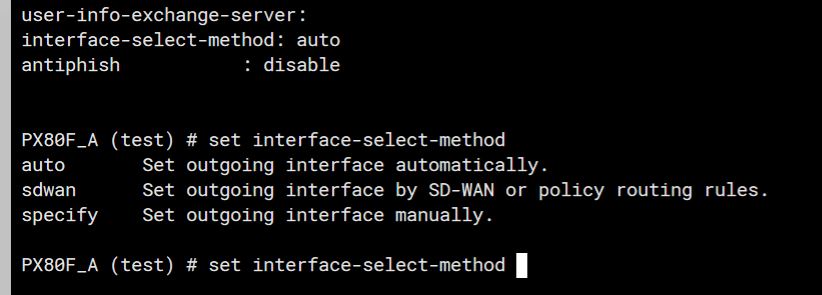
The trick here is to set the “interface-select-method” to sdwan. This resolved my issue and allowed things to start working. The reason it does this is that Self-originating traffic, such as Syslog, FortiAnalyzer logging, FortiGuard services, remote authentication, and others, relies on routing table lookups to determine the egress interface that is used to initiate the connection. Policy routes generated by SD-WAN rules do not apply to this traffic.
Fortigate FSSO and LDAP source IP
Posted by on December 16, 2015
I was presented with a scenario the other day where we had two sites connected with a Site-to-Site VPN. The VPN was up and working great, but FSSO and LDAP would not connect to servers on the other side of the VPN for lookups.
This made sense because I knew the fortigate was using its outside (Public) IP for lookups and obviously that was not in my Phase 2 subnets to encrypt. So how can I change this?
Note, these steps change the source IP that the FGT uses to query LDAP or FSSO.
There are options in both objects (FSSO, and LDAP) In CLI to change the source IP address. See below
LDAP Source IP change
First log in through CLI, and edit the object, Then set the source IP. Once you end the CLI session it should be changed.
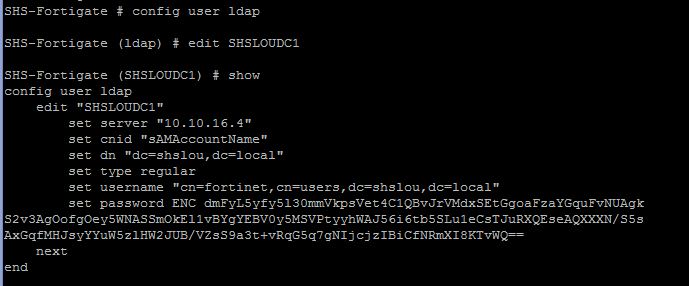
Now set the source IP address of the connection
![]()
Once you enter this and then end the session via the key word ‘end’ you will set the command.
Before moving on to the FSSO settings, here is a list of options available:
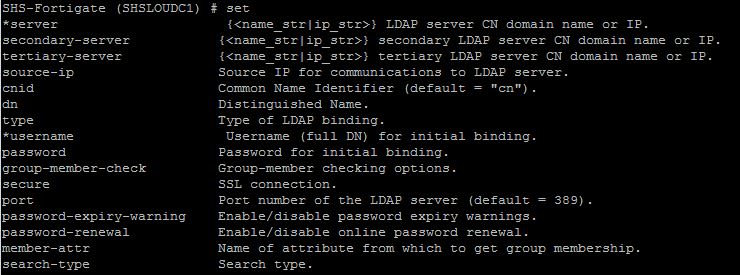
FSSO Source IP change
In CLI edit the FSSO object with the below commands, modify the source IP as below, and end the console to set the commands.

![]()
Once you enter this and then end the session via the key word ‘end’ you will set the command
That should be it! You modified your source IP to something in the encryption domain and it should now talk to the remote side and be able to do lookups.
Just in case below are all the options available under the FSSO.