Tag Archives: LDAP
Fortinet LDAP/RADIUS Source address with SD-WAN setup
Posted by on June 21, 2023
I found this a neat tidbit of knowledge that I thought I should share.
Created a Fortinet SDWAN setup with many sites – works awesome. Fortinet’s SDWAN is simple, but very effective with some really cool features to help with SLAs.
During this setup, I have Radius, and LDAP servers located across one of the members of the SDWAN (An IPSEC tunnel). As before with tunnels, you would modify the source address in CLI for the destination server. This would make sure requests originate from the interface you are expecting, and will go through the tunnel.
After switching the tunnel to be a member of a SDWAN interface the LDAP/RADIUS requests stopped working. I found another command was needed. This command is needed not only for Radius, and LDAP but also for FAZ, Fortiguard, and dns.
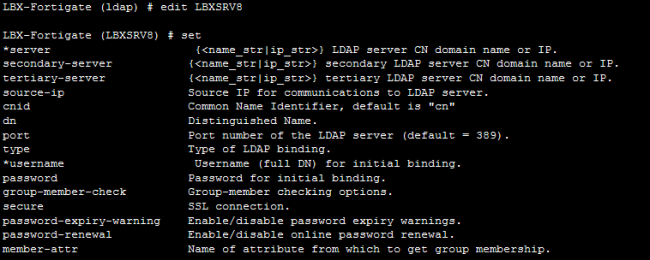
In CLI of both Radius and LDAP servers you will see these options:
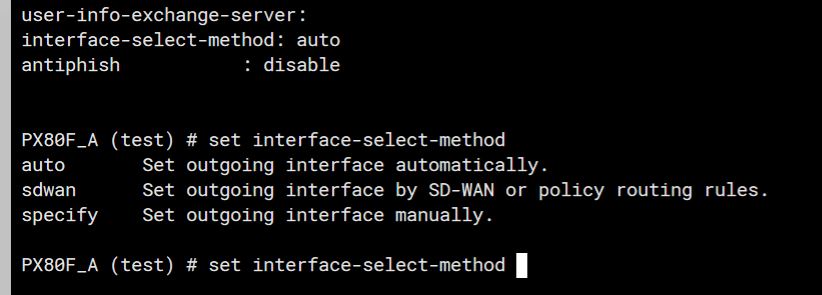
The trick here is to set the “interface-select-method” to sdwan. This resolved my issue and allowed things to start working. The reason it does this is that Self-originating traffic, such as Syslog, FortiAnalyzer logging, FortiGuard services, remote authentication, and others, relies on routing table lookups to determine the egress interface that is used to initiate the connection. Policy routes generated by SD-WAN rules do not apply to this traffic.
Fortigate SSL VPN Password expiration notification
Posted by on May 5, 2014
The Fortigate SSL is an amazing feature, but when users do not log in that often to any internal resources their AD password may expire and the user will not know. What really stinks is if that user has to post data for the month, and logs in at midnight for an 8 a.m. deadline! Luckily Fortigate has the ability to push the LDAP password expiration notification to the user, and can even let them change the password through SSL VPN login.
Steps:
– Get SSL VPN up and going with LDAP Authentication – This has to be an LDAPS connection to change the password, and your account to query LDAP has to be a domain admin!!!
– In CLI modify the LDAP server to allow password expiration notification, and change.
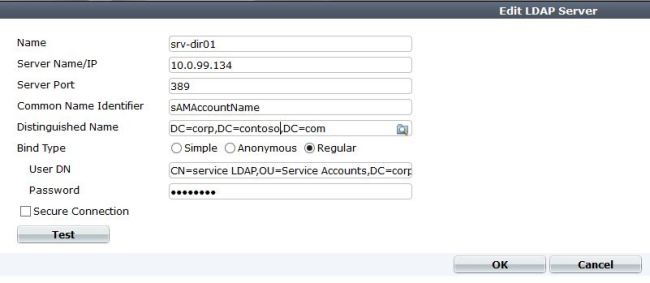
First create or modify your LDAP server in the GUI, and make sure its set to use LDAPS. The image below should be a good guide. Remember, the service account you use to query LDAP does not have to be an admin account, but if you want to change passwords then it does have to be a Domain-Admin. A good idea is to always create a service account to use for the Fortinet to query LDAP. That way if your admin password changes it will not affect this this account.
After that is configured, and tests/querys successfully then lets drop down to CLI and get the following configured.
Config user ldap
edit “Server name”
set password-expiry-warning enable
set password-renewal enable
end
For a look at all the options see picture below:
And that’s it, after this LDAP will push those messages to the client when they log in.
Remember, that the LDAP connection has to use SSL (LDAPS) to change the password.
Login to the Fortigate firewall with Active Directory accounts
Posted by on April 10, 2014
Logging into the firewall with Active directory accounts can be a great thing. You can base login privileges on A.D. security groups, and track what the users do. For example if you had help desk users and only wanted them to only have read access, no problem. Also, what if you wanted to audit what a user does on the firewall, no problem. You can do this through a mix of Logins and admin profiles.
There are a few things we need to do, create the LDAP connection, create our security groups in A.D. to match in the firewall, create the user group in the FW and assign it the correct admin profiles.
1. Create the LDAP connection
You do not have to be a super user to query the LDAP account, I would just create a Fortinet service account, and use that to query with.
2. Create AD security groups. If you want domain admins to log in, great just match it in the firewall. If you have help desk users that you want to have restricted privilege than you would have to create that in A.D. and add the needed members.
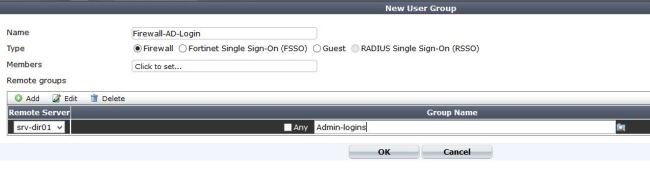
3. Create local firewall groups that match the LDAP groups.
Here we create a “Firewall” Group, and add our remote server to the list. If you notice you can query LDAP from here, and select the group you want by clicking on the folder to the left side of the group name.
4. Add the group as a admin that can login
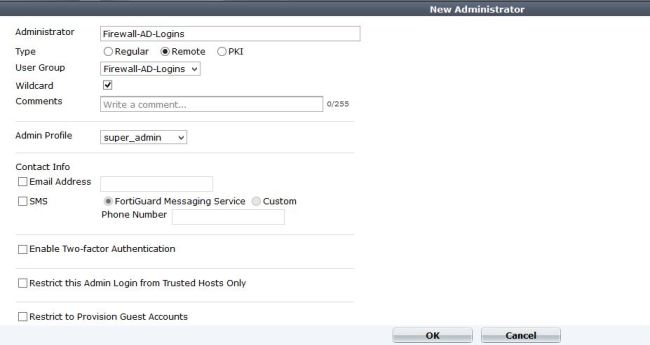
Under system – admin – administrators add a new admin.
Create the name you want, and select the group we just created. Then select the admin profile we want. This is for admins, so they will be super admins when they log in. If you wanted a custom profile, lets say restart the device, but that’s it then we can create that, then add it. There are more options here such as using Forti-token, and email.
Notice that the wildcard option is checked – A wildcard admin account is an administrator account with the wildcard option enabled. This option allows multiple different remote administration accounts to match one local administration account, avoiding the need to set up individual admin accounts on the FortiGate unit. Instead multiple LDAP admin accounts will all be able to use one FortiGate admin account.
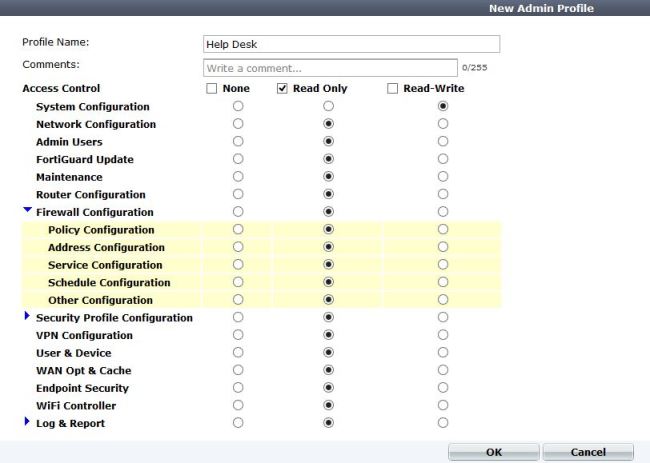
5. Create a different admin profile for privileges.
In this example I will create a help desk account, that can only configure system settings (IP address, etc). Otherwise everything is read only.
After saving this, you can go back and add it to the admin group.