Before learning the more about Manual or “Twice Nat” I would use individual object NAT (Auto NAT) for my incoming services, and use Manual NAT for my No-NAT or if I had to NAT VPN traffic before encryption (Policy NAT).
Recently though I started using it for everything. Once you get the hang of it, it is much more applicable to everyday NAT needs.
Something to note about Manual NAT:
- Processed before Auto NAT (Nat under the object command)
- Considers source, or source and destination together (Policy)
- For example – I need to NAT traffic to this IP, only when it goes to this network
- Configured directly from global config
- Uses objects only, cannot specify direct IPs
- Can specify to come after auto NAT.
Lets get started with a few examples. A list of all examples is below:
Static NAT – Public address/server to Private address/service
Group/Range of services forwarded into private server
Port redirection
Dynamic NAT
Policy Based Nat
Something to always note – 8.3 and above firmware’s require you to put in the private or real ip address of destination , not the public or Natted address.
Static NAT – Public address/server to Private address/service
Lets say my internal web servers is at 10.20.20.10. The external IP I am using is 23.4.3.10. I want to NAT in only HTTP (80) traffic to my server. No problem.
Lets create the our address Objects
object service OBJ-TCP-80
service tcp source eq 80
object network OBJ-10.20.20.10
host 10.20.20.10
object network OBJ-23.4.3.10
host 23.4.3.10
Great! Now lets create our Manual nat rule to allow that traffic in.
nat (inside,outside) source static OBJ-10.20.20.10 23.4.3.10 service OBJ-TCP-80 OBJ-TCP-80
Thats it, we would create our ACL to allow traffic to the Private host (Remember that, big time change in 8.3) and that’s it. Our traffic would be natted from Public, to Private port 80.
The next example will be a 1 to 1 NAT from our private object created above, to our public object also created above.
NAT (inside,outside) source static OBJ-10.20.20.10 OBJ-23.4.3.10
Modify the ACL to allow traffic to 10.20.20.10 and traffic should make it to the host.
Forward in a group or range of services
In this example we will forward in a group of service objects. Lets say HTTP, HTTPS, and SSH . Still using our local/public hosts. You have two options, 1 create a service group full of existing objects, or create a group of Service-objects. Int the below example I will create a group of predefined objects. This is due to having so many different configurations of groups.
object service OBJ-TCP-80
service tcp source eq 80
object service OBJ-TCP-443
service tcp source eq 443
object service OBJ-TCP-22
service tcp source eq 22
object-group service Web-services
group-object OBJ-TCP-80
group-object OBJ-TCP-443
group-object OBJ-TCP-22
object network OBJ-10.20.20.10
host 10.20.20.10
object network OBJ-23.4.3.10
host 23.4.3.10
So now our NAT rule:
nat (inside,outside) source static OBJ-10.20.20.10 23.4.3.10 service Web-services Web-services
Port redirection
Sometimes we have the need to make a port such as 8080 on the outside go to our websever on the inside at port 80. The below example shows how to do that. In this example we will forward in port 8080 on our public IP to port 80 on our private webserver. First we need to create the objects for the service and networking addresses, and then apply the nat rule – an don’t forget our ACL. To help visualize whats happening here look at the format of the rule:
nat (source interface,destination interface) source static object ((private) IP) object ( Natted (Public IP)) service Private-Service Public-Service
object service OBJ-TCP-80
service tcp source eq 80
object service OBJ-TCP-8080
service tcp source eq 8080
object network OBJ-10.20.20.10
host 10.20.20.10
object network OBJ-23.4.3.10
host 23.4.3.10
So now our nat rule:
nat (inside,outside) source static OBJ-10.20.20.10 23.4.3.10 service OBJ-TCP-80 OBJ-TCP-8080
Dynamic NAT
I like to usually do this through Auto nat, but you can most definitely do this through Manual.
object network OBJ-10.0.0.0/8
host 10.0.0.0/8
nat (inside,outside) source dynamic OBJ-10.0.0.0/8 interface
You could also specify “any” instead of the internal address object, or specify the public IP you want to be natted to instead of “interface”.
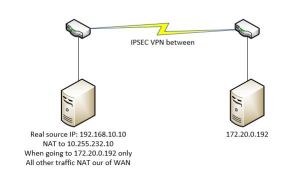
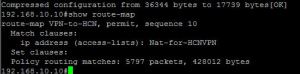
Policy Based manual NAT
Manual NAT is the only way I believe that Policy based natting is done. You would use this if you had to NAT traffic into some other IP when going to a certain destination address. In this example lets say we need to NAT traffic from 10.0.0.0/8 int 1.1.1.1 when going to destination 3.3.3.3. This comes up a lot in healthcare when both sides need to nat into a Public address so there are no address conflicts.
Lets first create our objects, then our Nat rule.
object network OBJ-10.0.0.0/8
host 10.0.0.0/8
object network OBJ-3.3.3.3
host 3.3.3
object network OBJ-1.1.1.1
host 1.1.1.1
So now our nat rule:
nat (inside,outside) source static OBJ-10.0.0.0/8 OBJ-1.1.1.1 destination static OBJ-3.3.3.3 OBJ-3.3.3.3
This reads that whenever 10.0.0.0/8 is going to 3.3.3.3, nat 10.0.0.0/8 into 1.1.1.1. This might help:
nat (inside,outside) source static Private-IP Natted-IP destination static Real-destination Natted-Destination
So, if this was used for a VPN you would just create an Crypto-ACL and the source would be your Natted-IP, and destination would be your 3.3.3.3 or whatever address lives across the tunnel that you set as your NAT destination.