The entry is written for a 90d, but will work the same for a 60d or 80d, even some C models.
By default the Fortigate is in “Switch mode” you will only be able to see the “internal” switch, and cannot add or remove interfaces from this switch. In this mode you can add more switches, but not remove the current ports.
In the next few parts we will change the switch mode to interface, and be able to add/remove ports and switches.
Before doing anything to the Firewall make a backup. When we actually change the interface mode it will delete the IP address on the internal interface. So connect to a WAN or DMZ port and use the GUI, or make sure to be consoled into the firewall VIA the serial port (console).
First we need to remove any reference to the “internal” switch itself. If you have a default config then there will be only two. The internal->WAN policy, and the DHCP server under the “Internal” interface.
You can see all references attached to the interface by navigating to System-Network-Interfaces and modifying the settings to show the Reference tab.

once those references show up, you can click on the number and navigate to the exact location of that reference. For example, let say you added an address object a long time ago and added the interface. Bingo – shows you exactly where.
After removing all the references by deleting them (yes, deleting.. so make a backup!) you should now see a 0 balance in the references. We can now change the interface mode in CLI.
You can either do this through a terminal such as putty, or through the GUI CLI app. Remember after changing the interface mode, it will delete your IP address on the internal network. So do this VIA Console, or go to the GUI on the WAN or DMZ interface.

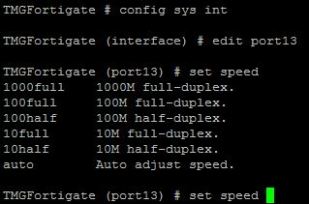
Commands are:
config system global
set internal-switch-mode interface
end
Then click y to reboot the firewall, when it comes back it will be in interface mode.
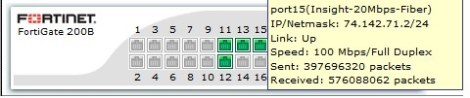
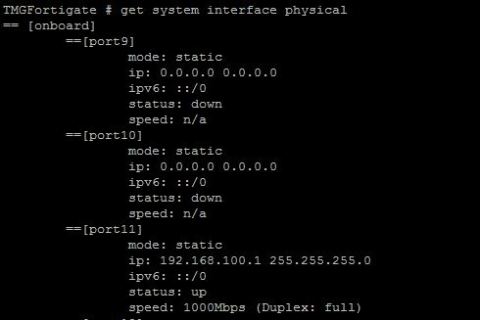
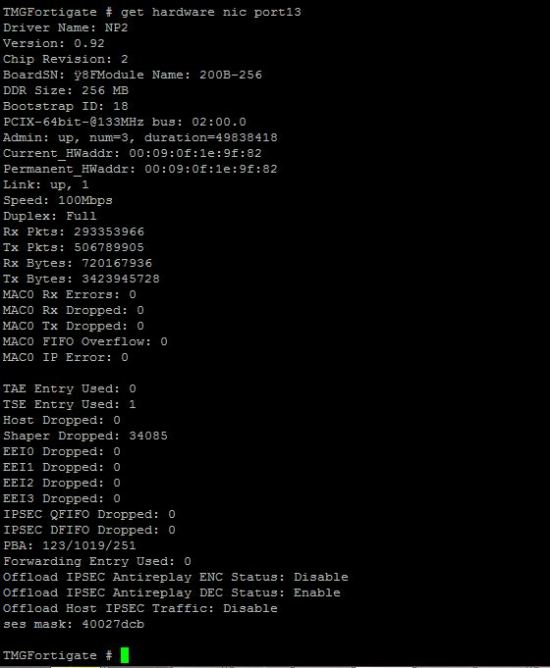
Once it is back up, login VIA the GUI on either the WAN1, WAN2, or DMZ ports. Then you should see something like this:

Now, under this page System-Network-Interfaces lets click the “Create” Button. From here you can create your switch. Select the type as Software or hardware switch depending on your model. You can also add your ports, set the name of the interface and the IP.

Once you press OK, you should see your new interface listed under system-network-interface as seen below

Recreate all of your policies, to allow access to and from and everything should work great. If you have any questions or I failed to explain anything please let me know.